A claimed $66 million crypto wallet recovery ended with zero funds recovered.
That’s the headline people remember. But it’s not the part I think matters most.
What matters is why a recovery story can get all the way to the finish line and still end with nothing. And for most crypto holders, the answer is less dramatic than they think. It usually comes down to basic self-custody confusion: what the device does, what the PIN does, what the seed phrase does, who had access to what, and how sloppy the chain of custody became before any recovery expert ever touched the wallet.
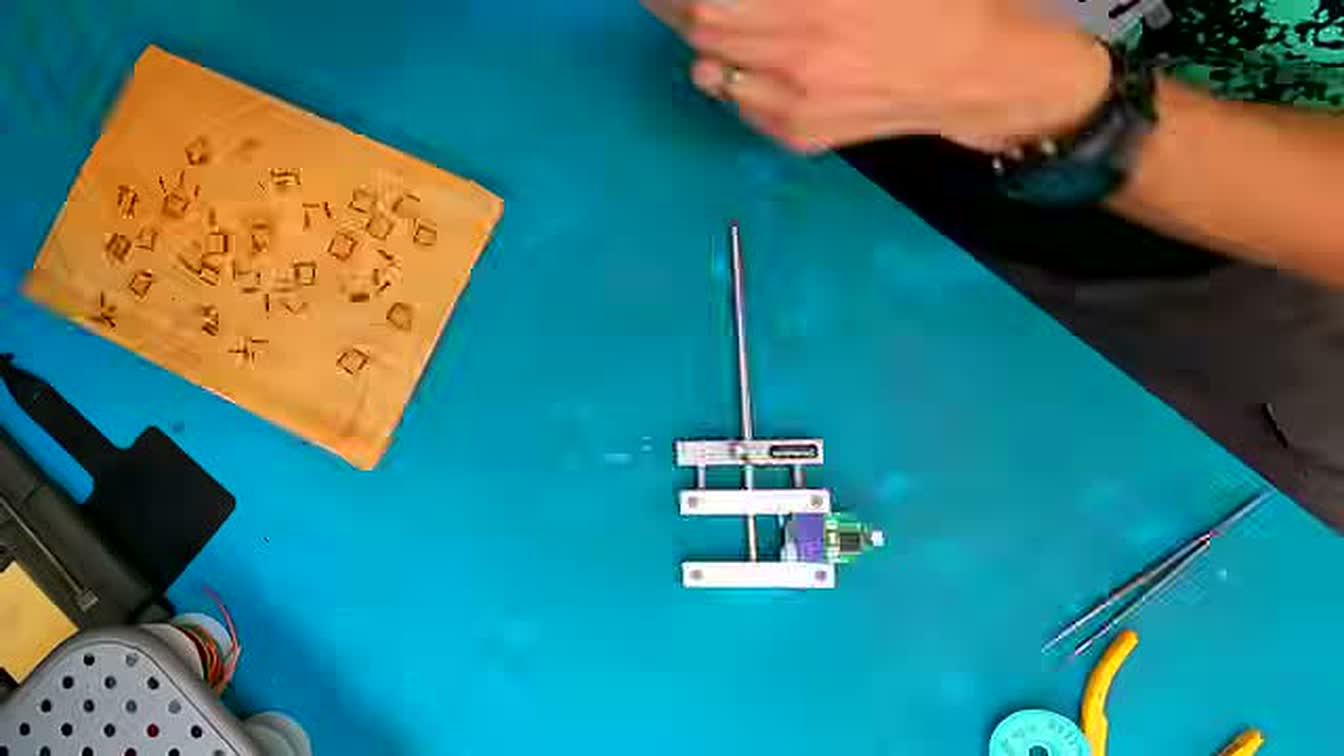
The case study here comes from Joe Grand’s video documenting a wallet recovery that appeared to involve roughly $66 million in crypto, only to end with a device showing zero funds and zero transaction history after the PIN was successfully cracked. If you want the original source, here it is: Joe Grand’s video on YouTube.
TLDR
- A recovered hardware-wallet PIN is not the same thing as recovered funds.
- The useful lesson here is device vs PIN vs seed phrase vs on-chain funds — not clickbait about a “hack.”
- If this story exposes holes in your setup, fix the process now: clean backup handling, fewer helpers, and a proper hardware-wallet workflow.
I’m not interested in turning this into a beat-by-beat recap. The useful takeaway is much simpler:
The real failure often happens before the recovery starts.
That’s the lesson I’d want every long-term crypto holder to understand.
The first thing to get straight: the wallet device is not the money
This is where a lot of beginners get lost.
People talk about a hardware wallet like it contains the money. It doesn’t. The funds live on-chain. The wallet device is a tool that helps you control the private keys needed to access those funds.
That distinction matters because it explains why a story like this can go sideways.
Here’s the cleanest way to think about it:
- The device is the physical hardware wallet
- The PIN unlocks access to that device locally
- The seed phrase is the real backup that can restore the wallet on another device
- The funds live on the blockchain, not “inside” the gadget
- A passphrase, if used, can create a completely different hidden wallet on top of the same seed phrase
If you mix those up, you’re going to make bad decisions.
That’s also why I keep saying self-custody is not just a product choice. It’s an operating procedure.
Why a recovered PIN can still lead to zero
In the Joe Grand case, the dramatic part is that the PIN was recovered and the result still came up empty.
Based on the video, Grand’s conclusion was that the device had likely been wiped and reinitialized before it got to him. In the video, he links that suspicion to the owner having previously handed the device to a friend who also tried to regain access. Once the recovery finished, the device reportedly showed zero transactions and zero funds.
That’s a brutal result, but it also teaches something important:
Recovering access is not the same as recovering value.
You can crack a PIN and still discover that the device state you now have access to is not the state you thought you were trying to recover.
That’s the part people miss.
They assume the hard part is getting into the hardware. Sometimes it is. But even a successful technical recovery can’t magically restore a clean custody history. If the wallet was wiped, reinitialized, or otherwise altered before the expert got it, the expert can only recover what’s actually there.
And if what’s there is a fresh state, then congratulations — you just recovered access to a wallet that no longer reflects the original one.
That’s not a hardware-wallet failure. That’s a process failure.
The expensive confusion: device vs PIN vs seed phrase
If you’ve been in crypto long enough, you start noticing that most people don’t lose money because the technology is too advanced. They lose money because they misunderstand which piece of information actually matters.
Let me make this painfully simple.
1. The device is replaceable
If you lose the hardware wallet but still have the correct seed phrase, you’re usually fine. You can restore the wallet on a new device.
That’s why I always say the hardware itself is not the backup.
2. The PIN is not the master key
The PIN protects the device from casual physical access. It matters. But it is not the same thing as owning the wallet.
A PIN is more like a lock on a door. Useful, necessary, but not the deed to the house.
3. The seed phrase is the real backup
Both Trezor and Ledger say versions of the same thing in their educational materials: the seed phrase / secret recovery phrase is the actual backup to the wallet, and if someone has it, they can restore the wallet elsewhere. Trezor’s documentation is especially blunt about this: the recovery seed is your only backup. Ledger says the seed phrase is the backup of all the private keys stored in the wallet.
That’s the real center of gravity in self-custody.
4. The funds are on-chain
This sounds obvious until people start acting like a damaged gadget means the money itself vanished. Usually it doesn’t. What matters is whether the keys can still be reconstructed.
But if the wallet setup was changed, reset, or recreated at some point, then what you can access now may not be what existed before.
And that’s where stories like this become ugly.
The real failure usually happens before the recovery call
This is the part the comments under videos usually understand better than the headlines do.
The failure often happens earlier, in the boring stage nobody pays attention to:
- when somebody writes the PIN and other notes in a confusing way
- when the seed phrase is lost, thrown away, or never verified
- when someone assumes they’ll “definitely remember it” later
- when a friend, ex, roommate, family member, or helper gets pulled into the process casually
- when multiple people try different recovery ideas without a clean chain of custody
- when the owner waits years and memory becomes part of the problem
That’s the actual lesson here.
By the time a high-end recovery specialist is involved, the damage may already be baked in. The expert is not stepping into a pristine forensic lab situation. He’s often stepping into a mess created by panic, memory gaps, partial notes, and too many hands touching the problem.
That’s why I don’t see this story as “look how crazy hardware wallets are.”
I see it as: look how unforgiving self-custody becomes when your process is vague.
Why chain-of-custody matters more than people think
This is the phrase I think more crypto holders need to learn: chain of custody.
In normal English, it just means knowing who had the device, who had the notes, who had the seed phrase, who tried what, and whether the wallet state may have been altered before the current recovery attempt.
If that history is messy, you’re operating half-blind.
In the source video, Grand’s explanation points back to prior access by another person and the possibility that the device was wiped and reinitialized before it ever reached him. I can’t prove more than the video proves, and neither can anybody else watching from the outside. That’s exactly why you have to be careful with the language.
But from a practical reader standpoint, the message is clear enough:
once other people start improvising with your wallet, your risk goes way up.
Not because every helper is malicious. Sometimes they’re just wrong. Sometimes they panic. Sometimes they try tools they don’t understand. Sometimes they make a mistake and then nobody has a clean record of what happened.
In crypto, “a friend took a look at it” is not the comforting sentence people think it is.
This is also why recovery is not the same as restitution
A lot of readers need this distinction hammered in.
A recovery expert might be able to:
- repair or access damaged hardware
- recover or crack a forgotten PIN
- extract data from a chip
- restore a wallet from valid recovery information
What they cannot do is guarantee that the funds you think should be there will still be there.
If the relevant seed phrase is gone, if a passphrase was involved and never documented, if the wallet was wiped, or if the funds were moved long before the recovery attempt, the technical recovery process can still end with zero.
That doesn’t mean the specialist failed.
It means self-custody failures are layered. By the time you see the final zero, the actual cause may be weeks, months, or years in the rearview mirror.
What I’d want every crypto holder to do differently after seeing this
If this story makes you uncomfortable, good. That means it’s doing its job.
Here’s the practical checklist I’d take from it.
1. Separate the concepts in your own head
If I asked you right now to explain the difference between your hardware wallet, your PIN, your seed phrase, and your passphrase, could you do it clearly?
If not, fix that first.
Confusion is not harmless in self-custody. Confusion is a risk factor.
2. Treat the seed phrase like the real backup, because it is
Write it down correctly. Keep it offline. Never put it in your phone notes, email drafts, cloud drive, or screenshots folder.
If you’re using self-custody for meaningful money, this is not the place to get lazy.
3. Verify your setup before the balance gets big
The worst time to discover your backup process is sloppy is after the wallet becomes life-changing money.
That’s why I prefer boring, deliberate setup over improvised genius. Set the wallet up correctly. Confirm what you wrote down. Understand how recovery works before you ever need it.
If you’re still holding long-term crypto on an exchange because your self-custody setup feels vague, I’d rather see you fix that with a proper hardware wallet workflow than keep punting the problem. If you want a straightforward option, you can check out Ledger here: Ledger hardware wallets.
4. Don’t let random helpers “try stuff” on a high-value wallet
I’m not saying never get help. I’m saying treat that decision with the seriousness it deserves.
If somebody else is involved, document exactly what they’re doing. Keep control of the process. Know whether they are troubleshooting, restoring, resetting, or experimenting. Those are not interchangeable actions.
“Maybe he can take a look” is a terrible recovery policy.
5. Build for memory failure, not memory confidence
Crypto holders love saying they’ll remember the PIN, or the variation, or the extra word, or where they put the backup.
Maybe. Maybe not.
People get older. Relationships end. Moves happen. Fires happen. Injuries happen. Stress wrecks recall. If your plan depends on perfect memory, it’s not a plan.
6. Give your future self a cleaner recovery path
A good self-custody setup should be understandable to future-you, not just current-you.
That means:
– clear offline backup handling
– clean labeling that doesn’t create more confusion
– a documented inheritance / emergency access plan
– less improvisation, more process
That’s the grown-up version of self-custody.
My actual takeaway from the $66 million story
The wrong lesson is: hardware wallets are dangerous.
The right lesson is: self-custody is operational.
A hardware wallet can be a smart move. In a lot of cases, I think it is a smart move. What it doesn’t do is save you from sloppy backup habits, fuzzy memory, trusted-person risk, or a broken chain of custody.
That’s why I don’t hear this story and think, “Wow, what a crazy hack.”
I think, “This is what happens when the process around the wallet matters more than the wallet itself.”
And honestly, that’s the part most crypto holders still underestimate.
If you want to take one action after reading this, make it simple: clean up your setup before it becomes a recovery story. If you need a hardware wallet to do that, start here with Ledger, then follow it with a proper cold-storage process and backup routine.
Because in crypto, the expensive mistakes usually don’t start with some cinematic hack.
They start with a note you didn’t verify, a backup you didn’t protect, or a person you trusted to “just take a look.”
Related reading
- How to Set Up a Ledger Hardware Wallet Step by Step
- How to Move Crypto to Cold Storage Safely
- Crypto Security Basics: 7 Things I Do to Protect My Portfolio
- Best Cold Wallets 2026: What I Use After Celsius Took My Money
This article uses Joe Grand’s video as a case study source. Where intent or exact prior wallet state can’t be independently verified from the outside, I’ve kept the framing to what the video shows or what Grand explicitly says in the video.